9 Document Management Best Practices for 2026
Discover 9 actionable document management best practices to streamline workflows, boost security, and enhance efficiency. Your essential guide for 2026.
In today's fast-paced business environment, managing documents effectively is no longer about keeping digital folders tidy; it's the backbone of organizational efficiency, security, and compliance. Disorganized files, rampant version confusion, and insecure access don't just waste employee time; they expose your business to significant operational and financial risks, from data breaches to compliance failures. Moving beyond a chaotic system of shared drives and email attachments is a critical step for any growing organization.
Overhauling your document strategy is a crucial step within the broader scope of applying essential business process improvement methods to enhance overall organizational efficiency. A robust document management system streamlines workflows, empowers teams with quick access to accurate information, and protects your most valuable digital assets. For small business owners, e-commerce operators, and SaaS product teams, getting this right means faster customer support, smoother operations, and more secure data handling.
This guide moves beyond generic advice to provide a comprehensive roundup of nine essential document management best practices. We will explore critical, actionable strategies that empower organizations to transform scattered files into a secure, searchable, and highly valuable asset. By implementing these practices, you can build a framework that not only solves today's challenges but also scales for future growth. You will learn how to ensure every piece of information is systematically organized, instantly accessible to the right people, and protected throughout its entire lifecycle. Let's dive into the strategies that will redefine how you handle your most critical information.
1. Implement a Centralized Document Repository
One of the most foundational document management best practices is establishing a single, centralized location for all organizational files. A centralized repository acts as the sole source of truth, eliminating the chaos of document silos where files are scattered across individual hard drives, email inboxes, and disparate cloud storage accounts. This approach ensures every team member accesses the most current version of a document, dramatically reducing version control errors and redundant work.
By unifying your digital assets, you create a cohesive ecosystem. This consolidation simplifies everything from security protocols to backup procedures, as you only have one system to manage and protect. Companies like NASA rely on this model for mission-critical specifications, ensuring that engineers, scientists, and administrators all work from the exact same plans.
Why It's a Critical First Step
A centralized system is the bedrock of an efficient document workflow. Without it, employees waste valuable time searching for files, questioning document authenticity, or recreating assets that already exist. Coca-Cola, for example, centralized its global marketing assets, reportedly cutting asset recreation costs by 40% because teams could easily find and reuse existing materials. A unified repository empowers your organization with powerful search capabilities, streamlined collaboration, and consistent access controls, forming the core of a secure and productive environment. To make an informed choice, it's helpful to start by comparing Content Management Systems like SharePoint to see which platform best fits your operational needs.
How to Implement a Centralized Repository
Successfully transitioning to a centralized system requires careful planning and phased execution.
- Start Small: Begin with a pilot program in a single, tech-savvy department to work out any kinks before a company-wide rollout.
- Prioritize Migration: Migrate documents in phases, starting with the most critical and frequently accessed files to deliver immediate value.
- Establish Structure First: Before moving a single file, define a logical folder structure and standardized naming conventions. This prevents the new system from becoming as disorganized as the old one.
- Invest in Training: Provide comprehensive user training and accessible support channels to ensure high adoption rates and correct usage from day one.
A well-implemented repository is more than just storage; it's a strategic asset that enhances security, boosts productivity, and provides a scalable foundation for growth. For a deeper dive into these platforms, you can learn more about choosing a documentation management system.
2. Establish Consistent Naming Conventions
Once a central repository is in place, the next critical step is creating and enforcing standardized rules for naming files and folders. Consistent naming conventions transform a chaotic digital archive into a logical, predictable system where anyone can find what they need quickly. This systematic approach ensures that files are easily identifiable, searchable, and organized, regardless of who created them or when.
Effective naming conventions are more than just a matter of tidiness; they are a core component of efficient document management best practices. They eliminate ambiguity and reduce the time employees spend deciphering cryptic file names. For instance, General Electric implemented standardized naming protocols that reportedly reduced document search time by over 60%, showcasing the immense productivity gains available. This practice ensures every document's purpose and context are clear at a glance.
Why It's a Foundational Practice
Without a defined naming standard, your document repository can quickly become a digital junk drawer. Employees revert to personal, often inconsistent, naming habits, making it nearly impossible to locate information efficiently or maintain version control. The UK's Government Digital Service established clear naming standards across all departments to ensure seamless interoperability and information exchange. A logical naming system is the human-readable equivalent of metadata, providing vital context that powers search, sorting, and automated workflows. It prevents the creation of duplicate files and ensures everyone is working from the correct version.
How to Implement Naming Conventions
Rolling out a successful naming convention requires clear rules, simple logic, and consistent enforcement.
- Keep it Simple: Design a convention that is intuitive and easy to remember. A common format is
[Date]_[DocumentType]_[Project/Client]_[Version], like2024-10-28_MarketingBrief_NewWebsite_v02. - Use a Consistent Date Format: Always use the
YYYY-MM-DDformat. This ensures files sort chronologically by default, making it easy to find the most recent documents. - Avoid Special Characters: Steer clear of characters like
&, *, %, #, /as they can cause errors in different operating systems and cloud platforms. Use hyphens or underscores instead of spaces. - Create a Reference Guide: Develop and distribute a one-page quick reference guide that outlines the naming rules with clear examples. Make it easily accessible to everyone in the organization.
- Automate Where Possible: Use tools within your document management system to enforce or suggest correct file names upon saving, which helps drive adoption and ensure compliance.
3. Implement Version Control Systems
Effective version control is a non-negotiable component of modern document management best practices, preventing the chaos of multiple document drafts circulating simultaneously. This systematic approach tracks and manages every change made to a document throughout its lifecycle. It ensures that every team member is working from the correct file, maintains a complete audit trail of who changed what and when, and allows you to revert to previous versions if needed.
By establishing clear protocols, version control eliminates the confusion of files named "Final_Report_v2_USE_THIS_ONE.docx." Instead, it creates a single source of truth that evolves predictably. Aerospace giant Airbus relies heavily on version control within its Product Lifecycle Management (PLM) systems for aircraft design documents. This precision prevents catastrophic engineering errors where a minor discrepancy could have multi-million dollar consequences.

Why It's a Critical Safeguard
Without version control, collaborative work becomes a high-risk activity. Errors, overwrites, and lost work are common, leading to significant wasted effort and a breakdown in quality control. For instance, legal firms like Baker McKenzie implement robust version control for contract management, reducing drafting errors and ensuring all parties are negotiating from the same document. It transforms a document from a static file into a living asset with a complete, transparent history, which is indispensable for compliance, audits, and collaborative integrity.
How to Implement Version Control
Integrating version control into your workflow requires both the right tools and clear, enforceable policies.
- Adopt Semantic Versioning: Use a clear numbering system like semantic versioning (e.g., v1.0 for major releases, v1.1 for minor updates, v1.1.1 for small fixes). This provides immediate context about the significance of a change.
- Leverage Built-In Tools: Most modern document management systems, like Google Docs and Microsoft SharePoint, have powerful built-in revision history and versioning features. Activate and configure these tools first.
- Establish Check-In/Check-Out Rules: For documents requiring exclusive editing, train users on proper check-in/check-out procedures. This locks a file while one person is working on it, preventing conflicting edits.
- Define Major Version Triggers: Create clear guidelines for when a document should be escalated to a new major version, such as after a key stakeholder approval or at a project milestone.
4. Define Clear Access Controls and Permissions
One of the most critical document management best practices is implementing granular security measures that control who can view, edit, share, and delete files. Defining clear access controls ensures sensitive information remains protected by adhering to the principle of least privilege, which grants users only the minimum access necessary to perform their jobs. This practice is essential for preventing unauthorized access, data breaches, and accidental data loss while still enabling secure collaboration.
By establishing role-based permissions, you create a structured security framework that is both effective and scalable. This approach is non-negotiable in regulated industries. For example, financial services firms implement strict, SOX-compliant document access for financial reporting, while healthcare organizations like Mayo Clinic use HIPAA-compliant controls to safeguard patient records, ensuring only authorized medical personnel can access sensitive health information.

Why It's a Critical Security Layer
Without robust access controls, your centralized repository becomes a high-risk liability. Unrestricted access means a single compromised account could expose the entire organization's data, from proprietary trade secrets to confidential client information. Law firms, for instance, depend on client-matter-based access controls to maintain attorney-client privilege and prevent conflicts of interest. Implementing these controls is fundamental to building a secure digital environment, meeting compliance requirements like GDPR and SOX, and fostering trust with clients and partners. This is a core component of a holistic security strategy, and you can explore more of these in this guide to the 10 best practices for data security.
How to Implement Clear Access Controls
Successfully deploying access controls requires a systematic and ongoing approach, not a one-time setup.
- Audit Existing Permissions: Start by analyzing current access rights to identify and revoke any excessive or unnecessary permissions.
- Use Group-Based Roles: Instead of assigning permissions to individuals, create user groups based on roles or departments (e.g., "Marketing Team," "Finance Auditors"). This simplifies management and reduces errors.
- Implement Automatic Inheritance: Configure your folder structure so that new files automatically inherit the permissions of their parent folder, ensuring consistency.
- Review and Recertify Regularly: Schedule periodic reviews (e.g., quarterly or semi-annually) to audit user permissions and ensure they remain appropriate as roles change.
5. Create Comprehensive Metadata and Tagging Systems
Beyond a logical folder structure, implementing a comprehensive metadata and tagging system is one of the most powerful document management best practices for discoverability. Metadata, which is essentially "data about data," provides context, describing a document's content, author, creation date, and status. This rich layer of information transforms your repository from a simple storage unit into an intelligent, searchable database.
Effective tagging systems, both manual and automated, allow users to find files based on concepts, projects, or status, not just filenames. For example, a pharmaceutical company like Pfizer uses meticulous metadata for drug development documents to track every stage, ensuring strict regulatory compliance and audit readiness. This systematic approach ensures the right information is retrievable in seconds, not hours.
Why It's a Critical Layer of Organization
A system without metadata relies solely on folder hierarchies and filenames, which are often inconsistent and subjective. This leads to lost files and wasted time. By adding descriptive tags, you create multiple pathways to find the same document, catering to different search behaviors. Reuters, the international news organization, implemented a comprehensive tagging system for its vast library of articles and images, reportedly reducing content discovery time by over 70% and allowing journalists to rapidly find relevant historical context for breaking stories.
How to Implement Metadata and Tagging
Building a useful metadata system requires a strategic and standardized approach to avoid creating more chaos.
- Start with Core Fields: Begin by defining a small set of essential, mandatory metadata fields like 'Document Type', 'Author', 'Status' (e.g., Draft, Final), and 'Project Name'.
- Use Controlled Vocabularies: For key fields, use predefined dropdown lists or controlled vocabularies instead of free-text entry. This ensures consistency and prevents variations like "Marketing" vs. "Mktg".
- Leverage Auto-Tagging: Implement tools that can automatically tag documents based on their content, title, or folder location to save time and ensure a baseline level of organization.
- Provide User Guidance: Offer tag suggestions based on similar documents or user history to encourage accurate and consistent tagging habits across the organization.
6. Establish Document Lifecycle Management
Effective document management extends beyond simple storage and retrieval; it involves overseeing a file’s entire journey from creation to disposal. Establishing a document lifecycle management (DLM) process provides a systematic framework for handling documents at every stage: creation, review, approval, distribution, maintenance, archival, and eventual destruction. This comprehensive approach ensures that information remains relevant, secure, and compliant throughout its useful life.
By defining and automating this lifecycle, organizations can significantly reduce risks and costs. For instance, financial services firms like JPMorgan Chase rely on rigorous DLM to manage regulatory documents, ensuring they meet strict compliance and retention mandates. This proactive governance prevents the accumulation of outdated, unnecessary files, which not only clutter systems but also pose a security and legal liability.
The infographic below illustrates the core stages in a typical document lifecycle management workflow, from its initial creation to its final disposition.
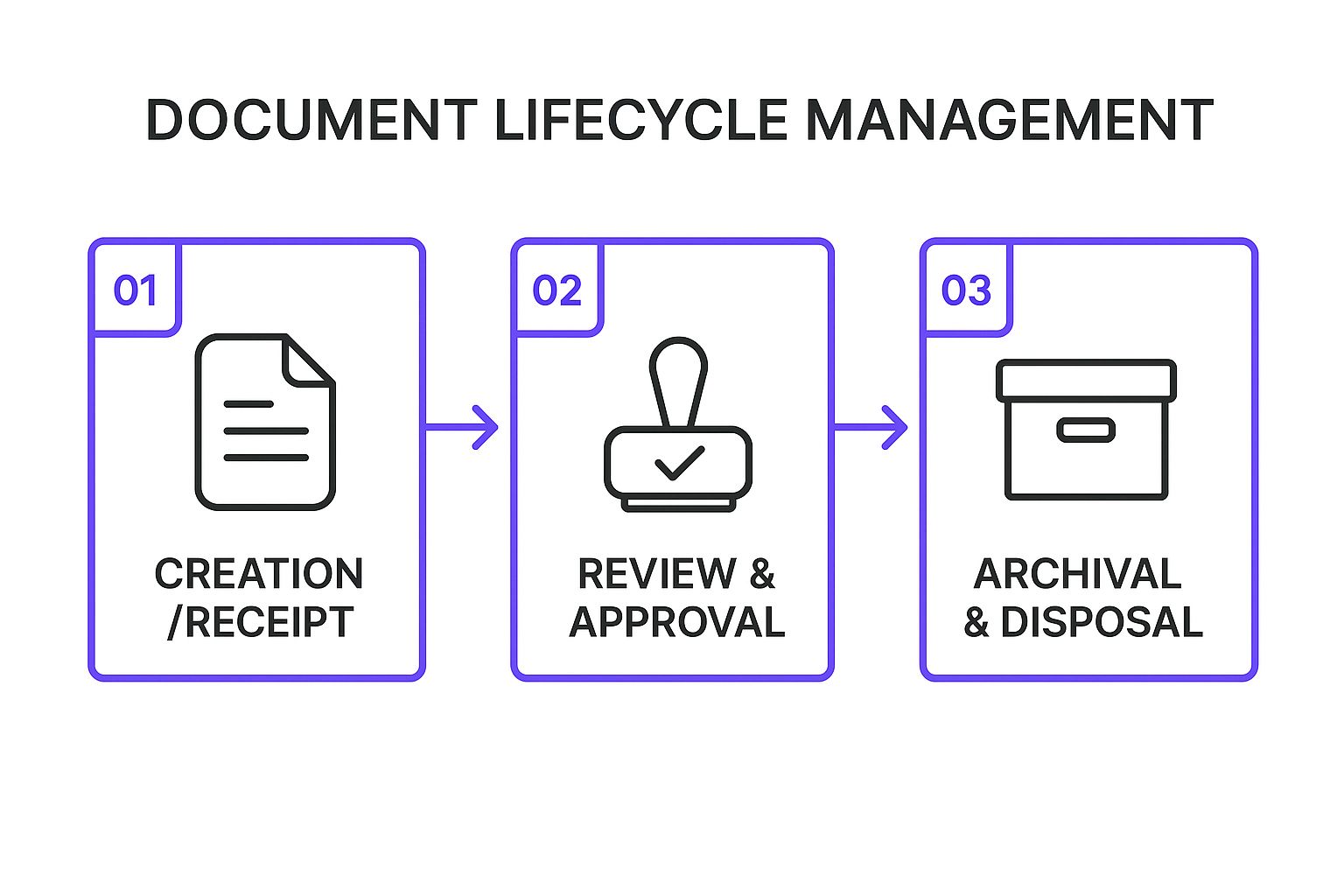
This streamlined flow ensures every document is actively managed, preventing it from becoming forgotten data that consumes storage and increases risk.
Why It's a Critical Step for Governance
Without formal lifecycle management, documents accumulate indefinitely, leading to bloated storage costs, inefficient search, and increased compliance risks. A well-defined lifecycle is a cornerstone of modern information governance. For example, government agencies are often required to follow strict records retention schedules mandated by entities like the National Archives to ensure public accountability and proper data handling. Implementing DLM transforms your documents from static files into managed assets with clear purpose, ownership, and a defined endpoint, which is a key principle detailed in data integration best practices.
How to Implement Document Lifecycle Management
A successful DLM strategy requires a clear plan that maps processes to your specific business needs and regulatory obligations.
- Map Document Types: Start by categorizing your documents (e.g., contracts, invoices, HR records) and mapping each category to a specific lifecycle workflow with defined stages and timelines.
- Automate Key Milestones: Use your document management system to set up automated notifications for critical events, such as upcoming contract renewal dates, policy review deadlines, and scheduled disposal dates.
- Define Clear Approval Chains: Establish formal review and approval workflows with designated primary and backup approvers to prevent bottlenecks and ensure accountability.
- Implement Retention Schedules: Create and enforce clear retention policies that dictate how long each document type must be kept. Integrate a legal hold feature to suspend disposal for documents relevant to litigation.
7. Implement Regular Backup and Disaster Recovery
A robust document management strategy is incomplete without a comprehensive plan for backup and disaster recovery. This practice involves creating secure, redundant copies of your digital assets to protect against loss from system failures, cyberattacks, human error, or natural disasters. The goal is to ensure business continuity by enabling rapid restoration of critical information, minimizing downtime and potential revenue loss.
Modern approaches have moved beyond simple nightly backups to local servers. Cloud-based solutions now offer real-time synchronization and geographically distributed storage, ensuring that even a catastrophic event at your primary location won't result in permanent data loss. After Hurricane Sandy, for instance, businesses with effective cloud backup strategies recovered their operations 300% faster than those relying solely on local backups, highlighting the resilience of a well-designed recovery plan.
Why It's a Critical Safeguard
Without a tested recovery plan, a single event can wipe out years of valuable data, intellectual property, and operational records. Proactive backups are your organization's ultimate insurance policy. Marriott Hotels demonstrated the power of this practice during a 2017 cyberattack; their established backup protocols allowed them to restore essential operational documents within hours, mitigating the impact on guest services and business functions. This proactive stance is a core component of effective document management best practices.
How to Implement Backup and Recovery
A successful strategy is built on systematic procedures and regular testing, not just technology.
- Follow the 3-2-1 Rule: Maintain at least three copies of your data, store them on two different types of media (e.g., cloud and a local hard drive), and keep at least one copy offsite.
- Automate Everything: Use automated backup software to eliminate human error and ensure consistency. Schedule incremental backups during off-hours to capture changes without disrupting workflow.
- Test Recovery, Not Just Backups: A backup is useless if it can't be restored. Regularly test your recovery procedures by performing trial restorations to verify data integrity and confirm your team knows the process.
- Encrypt Your Backups: Protect your data both in transit and at rest. Encrypting backups ensures that even if unauthorized parties gain access to the storage media, the information remains unreadable.
8. Enable Advanced Search and Retrieval Capabilities
A document management system is only as valuable as the information you can retrieve from it. Implementing powerful search capabilities transforms your repository from a passive storage unit into an active knowledge base, allowing users to find files instantly. This best practice involves moving beyond simple filename searches to technologies like full-text content indexing, metadata filtering, and AI-powered recommendations. This allows users to find what they need even if they don’t know the exact file name or location.
Advanced search helps users discover relevant content based on context, not just keywords. For example, Thomson Reuters implemented an AI-powered legal research platform that significantly reduces the time attorneys spend searching for case precedents. Similarly, NASA’s internal system lets engineers find highly specific technical specifications across millions of documents in seconds, a critical function for complex missions. These systems ensure that valuable information is always accessible, not lost in a digital abyss.
Why It's a Critical Efficiency Booster
Without advanced search, employees waste countless hours manually sifting through folders, a process that is both frustrating and inefficient. An effective search function is a cornerstone of modern document management best practices because it directly boosts productivity by minimizing friction between a user's question and the answer stored in a document. Google’s enterprise search tools, for instance, allow employees to find internal documents as easily as they search the web, demonstrating the power of an intuitive and powerful retrieval system. This immediate access to information accelerates decision-making, reduces duplicate work, and fosters a more informed workforce.
How to Implement Advanced Search
Deploying a robust search function requires a strategic approach focused on user needs and continuous improvement.
- Implement Full-Text Indexing: Ensure your system indexes the entire content of documents, not just titles and metadata. This allows users to search for specific phrases or data points within files.
- Utilize Faceted Search: Allow users to filter results based on multiple criteria like author, date created, document type, or project tag. This helps narrow down large result sets quickly.
- Leverage AI and Machine Learning: Implement tools that offer features like natural language processing for conversational queries, similarity matching to find related documents, and predictive suggestions that improve relevance over time.
- Analyze Search Behavior: Use search analytics to understand what users are looking for and whether they are successful. This data provides invaluable insights for optimizing the system and identifying content gaps.
9. Conduct Regular Audits and Compliance Reviews
Implementing a document management system is not a one-time project; it is an ongoing commitment to security and efficiency. One of the most critical document management best practices is conducting regular audits and compliance reviews. This involves systematically examining your systems, policies, and user activities to ensure they align with internal standards and external regulations, identify vulnerabilities, and optimize performance.
Regular audits act as a health check for your entire document ecosystem. They help maintain data integrity, enforce security protocols, and prove due diligence to regulatory bodies. For instance, healthcare organizations perform routine HIPAA compliance audits to protect patient information, a process that helps them avoid millions in potential fines. Similarly, financial firms like Goldman Sachs use continuous monitoring to maintain strict SEC compliance and safeguard sensitive client data.
Why It's a Critical Ongoing Process
Without regular audits, even the best document management system can degrade over time. Permissions become bloated, security gaps emerge, and user habits may deviate from established policies, creating significant risk. A proactive audit schedule prevents these issues from escalating into costly data breaches or compliance failures. PwC, a global professional services network, conducts quarterly document management audits that have reportedly prevented multiple compliance violations by catching procedural drift and access control issues before they become critical. These reviews are essential for any organization handling sensitive information, ensuring the system remains secure, efficient, and legally sound.
How to Implement Regular Audits
A successful audit program is built on a clear, repeatable framework that combines technology and procedural discipline.
- Create Standardized Checklists: Develop detailed audit checklists covering access controls, data classification, retention policy adherence, and security protocols. This ensures consistency across all reviews.
- Schedule Access Reviews: Plan quarterly or semi-annual reviews to verify user permissions. Promptly revoke access for employees who have changed roles or left the company to enforce the principle of least privilege.
- Use Automated Monitoring: Leverage built-in system tools or third-party software to continuously monitor for suspicious activity, such as bulk downloads or unauthorized access attempts.
- Document Everything: Meticulously record all audit findings, remediation steps taken, and the individuals responsible. This documentation is crucial for demonstrating compliance to external auditors and regulators.
9 Best Practices Comparison Guide
| Item | Implementation Complexity | Resource Requirements | Expected Outcomes | Ideal Use Cases | Key Advantages |
|---|---|---|---|---|---|
| Implement a Centralized Document Repository | Medium to High - requires migration and infrastructure setup | Significant initial migration effort, IT resources for hosting and maintenance | Unified access, reduced duplicates, improved collaboration | Organizations needing unified document access and control | Eliminates version confusion, standardizes access and backup |
| Establish Consistent Naming Conventions | Low to Medium - involves policy creation and enforcement | Moderate time investment, ongoing monitoring | Improved searchability and organization | Organizations struggling with file identification and editing workflows | Reduces search time, prevents duplicates, supports automation |
| Implement Version Control Systems | Medium - requires system setup and user training | Requires versioning tools, user discipline | Clear version history, safer collaboration | Collaborative environments with frequent document edits | Eliminates version conflicts, full audit trails, rollback ability |
| Define Clear Access Controls and Permissions | Medium to High - complex setup and ongoing management | IT resources for security setup, continuous audits | Secured sensitive info, regulatory compliance | Organizations handling sensitive or regulated data | Protects data, enforces least privilege, supports audit trails |
| Create Comprehensive Metadata and Tagging Systems | Medium - needs taxonomy design and user training | Time for system design, maintenance, and training | Enhanced discoverability and filtering | Large document collections requiring easy retrieval | Improves search precision, supports workflows, aids compliance |
| Establish Document Lifecycle Management | High - requires detailed process design and monitoring | Significant upfront planning and process resources | Current, compliant documents; cost reduction | Regulated industries and organizations with long document retention | Reduces storage costs, ensures compliance, improves quality control |
| Implement Regular Backup and Disaster Recovery | Medium - technical setup with ongoing testing and monitoring | Infrastructure for backups, storage costs | Data protection, business continuity | All organizations requiring data loss prevention | Protects against data loss, supports rapid recovery, compliance support |
| Enable Advanced Search and Retrieval Capabilities | High - complex integration and resource intensive | Strong processing power, indexing systems | Fast, accurate document retrieval | Organizations with large, diverse document repositories | Reduces search time, supports AI recommendations, boosts productivity |
| Conduct Regular Audits and Compliance Reviews | Medium to High - requires expertise and process adherence | Dedicated personnel and automated audit tools | Maintained compliance and optimized systems | Highly regulated sectors or organizations seeking continuous compliance | Detects vulnerabilities, improves processes, ensures legal compliance |
From Chaos to Control: Your Next Steps in Document Mastery
Navigating the complex landscape of digital information can feel like a perpetual battle against chaos. We've explored a comprehensive suite of document management best practices, moving from foundational principles like centralized repositories and consistent naming conventions to more advanced strategies involving version control, lifecycle management, and regular compliance audits. Each practice serves as a critical building block in constructing a fortress of efficiency, security, and accessibility around your organization's most valuable asset: its information.
The journey from scattered files and ambiguous versions to a streamlined, intelligent system is not an overnight sprint; it is a strategic marathon. The principles outlined in this guide, from implementing granular access controls to enabling robust search capabilities, are designed to work in synergy. They collectively transform your document ecosystem from a passive storage unit into an active, dynamic hub for knowledge and collaboration.
Recapping Your Path to Document Excellence
To truly internalize these concepts, let's distill the core journey we've mapped out. You've learned the immense value of:
- Creating a Single Source of Truth: Centralizing documents eliminates the guesswork and wasted hours spent hunting for the correct file across disparate systems. It’s the foundational step upon which all other practices are built.
- Building a Common Language: Standardized naming conventions and comprehensive metadata act as a universal translator for your entire team, ensuring everyone can find, understand, and categorize information with absolute clarity.
- Securing and Controlling Information Flow: Version control, access permissions, and lifecycle management are the guardians of your data's integrity. They prevent unauthorized access, stop accidental overwrites, and ensure documents are managed appropriately from creation to archival.
- Ensuring Resilience and Compliance: Regular backups, disaster recovery plans, and systematic audits are not just "nice-to-haves"; they are your organization's insurance policy against data loss, security breaches, and costly regulatory non-compliance.
Mastering these document management best practices does more than just tidy up your digital folders. It directly translates into measurable business outcomes. You empower your team with immediate access to the right information, accelerate decision-making, significantly reduce security risks, and build a scalable foundation for future growth.
Your Action Plan: Making It Happen
Theory is powerful, but action is transformative. The most common pitfall is trying to implement everything at once. Instead, adopt a phased, strategic approach to ensure lasting success.
- Start with the Highest Impact: Identify your biggest pain point. Is it finding files? Begin by implementing a central repository and establishing clear naming conventions. Are you concerned about security? Prioritize defining access controls and permissions.
- Gain Team Buy-In: Document management is a team sport. Host a workshop to explain the "why" behind the new processes. Demonstrate the time-saving benefits and gather feedback to refine the system, fostering a culture of ownership.
- Leverage Technology Wisely: You don’t have to build this system from scratch. A modern Document Management System (DMS) can automate versioning, access controls, and lifecycle policies. Invest in a tool that aligns with your specific needs.
- Iterate and Improve: Your system should not be static. Schedule quarterly reviews to assess what’s working and what isn’t. Is a naming convention too complex? Are access levels too restrictive? Adapt based on real-world usage and feedback.
Ultimately, the goal is to shift your organization's relationship with its documents. Files should not be seen as static artifacts to be stored and forgotten. They are living assets, filled with insights, knowledge, and critical data. The true evolution in document management lies not just in organizing this information, but in activating it. Imagine a world where your team no longer needs to hunt through folders to find an answer. Instead, they can simply ask a question and get an instant, accurate response sourced directly from your controlled repository. This is the future, and it's more accessible than ever. By committing to these document management best practices, you are laying the groundwork for a more intelligent, responsive, and data-driven organization.
Ready to transform your organized documents into an on-demand knowledge engine? Whisperchat.ai builds a secure AI chatbot directly from your documentation, allowing your team and customers to get instant, accurate answers without ever searching for a file. Stop managing documents and start activating your knowledge by visiting Whisperchat.ai to see how it works.